Admin Deployment
The English user guide is currently in beta preview. Most of the documents have been automatically translated from the Japanese version. Should you find any inaccuracies, please reach out to Flatt Security.
We provide deployment scripts for setting up Takumi Guard across your organization's developer machines using management tools. Customize them to suit your management tool.
This feature requires an active base subscription with Guard enabled. See Pricing & Billing for details.
Overview
The setup consists of two phases:
- Preparation — Create a bot in Shisho Cloud console and download the setup script
- Deployment — Create a wrapper script for your management tool and push it along with the setup script to target machines
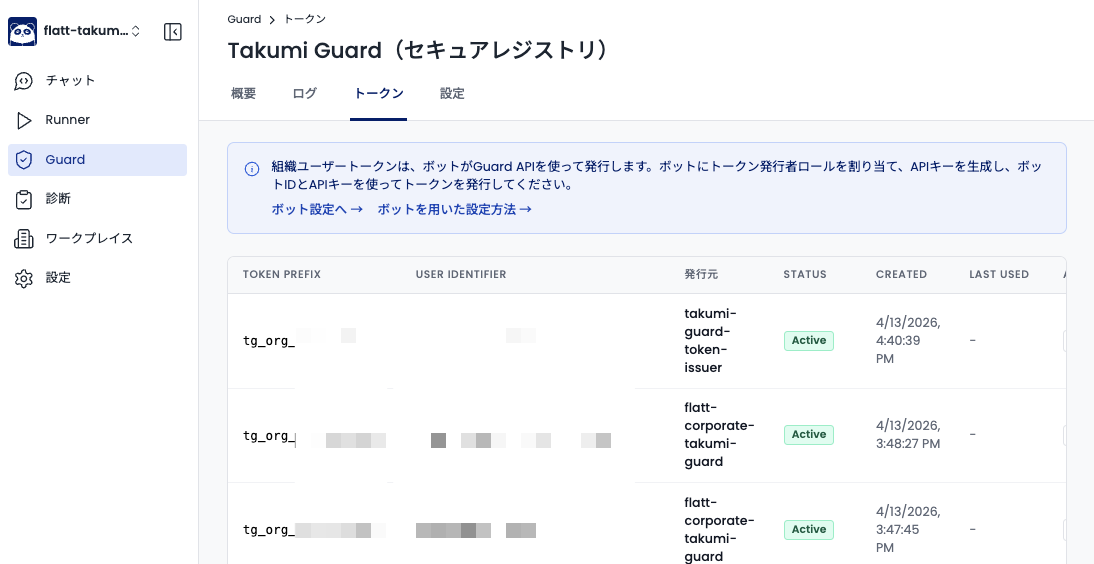
Tokens issued by the setup script can be viewed and managed in the Shisho Cloud console under Guard > Tokens.
Prerequisites
Before deploying, complete the following steps in Shisho Cloud console:
- Create a bot — Click the "Add Bot" button on the Settings > Bots page
- Assign the role — Select the "Takumi Guard Token Issuer" role for the bot
- Get the API key — On the bot's detail page, click "Create API Key" and save it securely
For detailed instructions on creating bots and API keys, see this guide.
Setup Script
We provide a setup script that handles token minting and package manager configuration. Download the script for your platform:
- macOS / Linux: https://shisho.dev/releases/takumi-guard-setup-0.5.0.sh
- Windows: https://shisho.dev/releases/takumi-guard-setup-0.5.0.ps1
Target machines must have curl installed (macOS and Linux).
Usage
The setup script only modifies config files for the user who runs it. To deploy across all users in your organization, use the wrapper scripts described in the Deployment Examples section.
Run the setup script as follows. Pass the API key via the TG_BOT_API_KEY environment variable:
TG_BOT_API_KEY="shisho_apikey_..." ./setup.sh <BOT_ID> <USER_IDENTIFIER>
| Parameter | Description |
|---|---|
TG_BOT_API_KEY | Bot API key (environment variable) |
BOT_ID | Bot ID from Shisho Cloud console |
USER_IDENTIFIER | A unique identifier for the device/user |
To limit which package managers are configured, pass the scope as the third argument.
TG_BOT_API_KEY="..." ./setup.sh BOT_ID USER_IDENTIFIER npm,rubygems
| Scope | Package managers configured |
|---|---|
npm | npm, pnpm, yarn (v2+), bun |
pypi | pip, uv, poetry |
rubygems | Bundler |
Choosing a USER_IDENTIFIER
The USER_IDENTIFIER is an opaque string that identifies a device or user. Choose a consistent naming convention for your organization.
Constraints:
- Allowed characters:
a-z,A-Z,0-9,-,_,.,@,+ - Length: 4 to 255 characters
Here are some examples of identifiers you can use.
| Example | Value | Description |
|---|---|---|
| Device serial number + OS username | C02X1234_jdoe | Hardware serial number from the device BIOS |
| Asset management ID + employee ID | ASSET0042_EMP12345 | IDs managed by your organization |
| MDM device ID + OS username | a401c7d0_jdoe | Device ID assigned by your MDM tool |
Verify that your chosen identifier is unique within your organization. Some identifiers (e.g., serial numbers) may be empty or not unique on certain environments such as custom-built PCs or virtual machines. Use a value that reliably distinguishes each device and user.
Behavior
First run
The setup script mints a token, creates a timestamped backup of each existing config file (e.g. ~/.npmrc-backup-20260408-162351), and appends Guard settings. Existing non-Guard settings are not modified.
Cases where the token is overwritten
The setup script inspects every Guard-managed config file and validates any existing token it detects. If different tokens are present across multiple config files, every one of them is validated.
If every detected token matches one of the following conditions, the script mints a fresh organization user token and overwrites the existing tokens with the new one. On the other hand, if at least one valid organization user token bound to the specified organization is found, that token is reused.
- An email-verified token
- A token that does not exist
- A token that has been revoked
- A token issued for a different organization
A timestamped backup of each config file is created before the overwrite.
Subsequent runs
The setup script detects the valid organization user token and reuses it, so a new token is not minted except in the cases above. Config files that already have Guard settings are also skipped (no changes, no backups). You can add new scopes incrementally — for example, run with npm first, then pypi later.
Manual rollback
The setup script creates a timestamped backup before modifying each config file (e.g. ~/.npmrc-backup-20260408-162351). To undo Guard settings, copy the backup file back to its original name (e.g. cp ~/.npmrc-backup-20260408-162351 ~/.npmrc).
Revoke tokens that are no longer needed (e.g., after device replacement or employee departure) from the Shisho Cloud console. See Revoking an Org User Token for the procedure.
If a package manager already has a different registry configured (e.g., a private npm registry), the setup script overwrites the existing registry with the Guard registry. A timestamped backup is created before each overwrite, but we recommend reviewing registry settings on target machines before deployment.
Deployment Examples: one token per user
The deployment method varies depending on your management tool and target OS. Below are common deployment patterns for each platform.
The wrapper scripts below are starting points. Real environments often need to exclude administrative service accounts, or users you don't want to configure Guard for. You can layer those filters directly into the wrapper.
macOS / Linux:
# Skip specific user names
case "$USER_NAME" in
corp-admin|service-account|Guest) continue ;;
esac
Windows:
# Skip specific user names
$Skip = @('corp-admin', 'Guest', 'defaultuser0')
if ($Skip -contains $UserName) { continue }
The same approach lets you narrow down by directory (/Users/dev-* only), by group membership (id -Gn "$USER_NAME" | grep -q developers), or by any other policy that fits your fleet.
macOS / Linux
Management tools typically execute scripts with root privileges. To deploy across all developers, use a wrapper script that switches to each user's context as shown below. On macOS, follow your management tool's script-distribution procedure (for example, Jamf Pro's Running Scripts guide).
To also configure Guard for the root user, run the setup script once without switching users inside the wrapper script.
macOS
#!/bin/bash
# Admin deployment wrapper
# TODO: Replace with your Bot ID and API key from Shisho Cloud console
BOT_ID="BTXXXXXXXXXXXXXXXXXXXXXXXXXX"
export TG_BOT_API_KEY="shisho_apikey_XXXXX"
# TODO: Update VERSION when a newer setup script becomes available
VERSION="0.5.0"
# Download the setup script
curl -sL -o /tmp/takumi-guard-setup.sh https://shisho.dev/releases/takumi-guard-setup-${VERSION}.sh
chmod 755 /tmp/takumi-guard-setup.sh
# Get the device serial number for USER_IDENTIFIER generation
SERIAL=$(ioreg -l | grep IOPlatformSerialNumber | awk -F'"' '{print $4}')
# Run the setup script for each user on this machine
for USER_HOME in /Users/*; do
USER_NAME=$(basename "$USER_HOME")
# Skip system directories and non-existent paths
[ "$USER_NAME" = "Shared" ] && continue
[ ! -d "$USER_HOME" ] && continue
# Skip if the user account does not exist
id "$USER_NAME" >/dev/null 2>&1 || continue
# Build a unique identifier for this device + user combination
USER_IDENTIFIER="${SERIAL}_${USER_NAME}"
# Run the setup script as this user.
# Use zsh -lic (login + interactive) so that ~/.zshrc is loaded and
# package managers installed outside the default PATH are found.
sudo -u "$USER_NAME" -H zsh -lic '
TG_BOT_API_KEY="'"$TG_BOT_API_KEY"'" \
/tmp/takumi-guard-setup.sh "'"$BOT_ID"'" "'"$USER_IDENTIFIER"'"
'
echo "[Done] $USER_NAME (USER_IDENTIFIER: $USER_IDENTIFIER)"
done
# Clean up credentials and temporary files
unset TG_BOT_API_KEY
rm -f /tmp/takumi-guard-setup.sh
Linux
#!/bin/bash
# Admin deployment wrapper
# TODO: Replace with your Bot ID and API key from Shisho Cloud console
BOT_ID="BTXXXXXXXXXXXXXXXXXXXXXXXXXX"
export TG_BOT_API_KEY="shisho_apikey_XXXXX"
# TODO: Update VERSION when a newer setup script becomes available
VERSION="0.5.0"
# Download the setup script
curl -sL -o /tmp/takumi-guard-setup.sh https://shisho.dev/releases/takumi-guard-setup-${VERSION}.sh
chmod 755 /tmp/takumi-guard-setup.sh
# Get the device serial number for USER_IDENTIFIER generation
SERIAL=$(dmidecode -s system-serial-number)
# Run the setup script for each user on this machine
for USER_HOME in /home/*; do
USER_NAME=$(basename "$USER_HOME")
# Skip non-existent paths
[ ! -d "$USER_HOME" ] && continue
# Skip if the user account does not exist
id "$USER_NAME" >/dev/null 2>&1 || continue
# Build a unique identifier for this device + user combination
USER_IDENTIFIER="${SERIAL}_${USER_NAME}"
# Run the setup script as this user.
# Detect the user's login shell and run it in login + interactive mode
# so that ~/.bashrc (or ~/.zshrc) is loaded and package managers
# installed outside the default PATH are found.
# Explicitly source .bashrc as a fallback for environments where
# .bash_profile does not source it (e.g. CentOS).
USER_SHELL=$(getent passwd "$USER_NAME" | cut -d: -f7)
sudo -u "$USER_NAME" -H "$USER_SHELL" -lic '
[ -f "$HOME/.bashrc" ] && . "$HOME/.bashrc" 2>/dev/null
TG_BOT_API_KEY="'"$TG_BOT_API_KEY"'" \
/tmp/takumi-guard-setup.sh "'"$BOT_ID"'" "'"$USER_IDENTIFIER"'"
'
echo "[Done] $USER_NAME (USER_IDENTIFIER: $USER_IDENTIFIER)"
done
# Clean up credentials and temporary files
unset TG_BOT_API_KEY
rm -f /tmp/takumi-guard-setup.sh
Windows
A Windows device typically has more than one user profile. Decide whether to apply Guard settings to every profile on the device or only to the currently logged-in user, then follow the matching procedure below.
- To apply to every user on the device: have your management tool run the wrapper as
SYSTEM. Microsoft Configuration Manager (formerly SCCM), Group Policy startup scripts, PDQ Deploy, and most other MDM tools do this by default. - To apply only to the logged-in user: have your management tool run the wrapper under the logged-on user's credentials. Microsoft Intune's "Run this script using the logged on credentials" option and Group Policy logon scripts fit this case.
Install for all users on the device
Save the script below and have your management tool push it to each device and run it as SYSTEM. Because SYSTEM privileges are required, distribution typically goes through your management tool rather than a side channel. The wrapper downloads the setup script and walks every user profile on the device via Win32_UserProfile, configuring each in turn.
# Admin deployment wrapper (all-users mode)
# Run as SYSTEM (or any administrator). Requires PowerShell 5.1 or later.
# TODO: Replace with your Bot ID and API key from Shisho Cloud console
$BotId = 'BTXXXXXXXXXXXXXXXXXXXXXXXXXX'
$env:TG_BOT_API_KEY = 'shisho_apikey_XXXXX'
# TODO: Update VERSION when a newer setup script becomes available
$Version = '0.5.0'
# Download the setup script
$ScriptPath = 'C:\Windows\Temp\takumi-guard-setup.ps1'
Invoke-WebRequest -Uri "https://shisho.dev/releases/takumi-guard-setup-$Version.ps1" `
-OutFile $ScriptPath -UseBasicParsing
# Get the device serial number for USER_IDENTIFIER generation
$Serial = (Get-CimInstance -ClassName Win32_BIOS).SerialNumber
# Run the setup script for each user profile on this machine.
# Win32_UserProfile excludes built-in service profiles (SYSTEM, LocalService,
# NetworkService) via `Special = false`. Profiles whose directories no longer
# exist (deleted users with leftover registry entries) are also filtered out.
foreach ($profile in (Get-CimInstance -ClassName Win32_UserProfile -Filter "Special = false" |
Where-Object { $_.LocalPath -and (Test-Path $_.LocalPath) })) {
$UserHome = $profile.LocalPath
$UserName = Split-Path $UserHome -Leaf
# Build a unique identifier for this device + user combination
$UserIdentifier = "${Serial}_${UserName}"
# Invoke setup.ps1 with USER_HOME pointing at this profile. The script
# resolves the profile owner from USER_HOME so that the resulting config
# files grant access to the target developer, not just SYSTEM.
$env:USER_HOME = $UserHome
try {
& powershell.exe -ExecutionPolicy Bypass -File $ScriptPath $BotId $UserIdentifier
} catch {
Write-Output "[Error] Failed for $UserName : $_"
} finally {
Remove-Item Env:USER_HOME -ErrorAction SilentlyContinue
}
Write-Output "[Done] $UserName (USER_IDENTIFIER: $UserIdentifier)"
}
# Clean up credentials and the temporary script
Remove-Item Env:TG_BOT_API_KEY -ErrorAction SilentlyContinue
Remove-Item $ScriptPath -Force -ErrorAction SilentlyContinue
Install for the logged-in user
Save the script below and deploy it to each device through your management tool, or distribute it via shared storage or another channel and ask each user to run it.
# Admin deployment wrapper (logged-in user mode)
# Run as the logged-in user. Requires PowerShell 5.1 or later.
# TODO: Replace with your Bot ID and API key from Shisho Cloud console
$BotId = 'BTXXXXXXXXXXXXXXXXXXXXXXXXXX'
$env:TG_BOT_API_KEY = 'shisho_apikey_XXXXX'
# TODO: Update VERSION when a newer setup script becomes available
$Version = '0.5.0'
# Download the setup script
$ScriptPath = Join-Path $env:TEMP 'takumi-guard-setup.ps1'
Invoke-WebRequest -Uri "https://shisho.dev/releases/takumi-guard-setup-$Version.ps1" `
-OutFile $ScriptPath -UseBasicParsing
# Build a unique identifier for this device + user combination
$Serial = (Get-CimInstance -ClassName Win32_BIOS).SerialNumber
$UserIdentifier = "${Serial}_${env:USERNAME}"
& powershell.exe -ExecutionPolicy Bypass -File $ScriptPath $BotId $UserIdentifier
# Clean up credentials and the temporary script
Remove-Item Env:TG_BOT_API_KEY -ErrorAction SilentlyContinue
Remove-Item $ScriptPath -Force -ErrorAction SilentlyContinue
The default Windows execution policy blocks unsigned .ps1 scripts, so the wrappers above need to be invoked with execution policy bypass. Microsoft Intune, Microsoft Configuration Manager, and Group Policy startup scripts all run PowerShell scripts this way out of the box, so no extra configuration is required. Only when invoking the wrapper manually (for example, from PsExec) do you need to call it as powershell.exe -ExecutionPolicy Bypass -File <your-wrapper>.ps1.
Deployment Examples: one token per device
The wrappers in the previous section mint one token per (device, user) pair. On devices that host multiple developer accounts (shared workstations, MDM-managed administrator account alongside a regular user, IdP-provisioned profile coexisting with a built-in local account, ...), this consumes one license per account on the same machine.
If you want one billed token per device instead, use the wrappers below. Each one discovers an existing active Guard token anywhere on the device first, mints one only if needed, and then installs the same token for every developer account. Both this section's wrappers and the previous section's reuse a valid token on subsequent runs, so periodic re-execution stays safe with either model.
macOS
#!/bin/bash
# Admin deployment wrapper (one token per device)
# TODO: Replace with your Bot ID and API key from Shisho Cloud console
BOT_ID="BTXXXXXXXXXXXXXXXXXXXXXXXXXX"
export TG_BOT_API_KEY="shisho_apikey_XXXXX"
# TODO: Update VERSION when a newer setup script becomes available
VERSION="0.5.0"
# Download the setup script
curl -sL -o /tmp/takumi-guard-setup.sh "https://shisho.dev/releases/takumi-guard-setup-${VERSION}.sh"
chmod 755 /tmp/takumi-guard-setup.sh
# Device-level USER_IDENTIFIER: serial number only -- the token is shared
# across every user on this device, so the identifier does not embed a user.
SERIAL=$(ioreg -l | grep IOPlatformSerialNumber | awk -F'"' '{print $4}')
USER_IDENTIFIER="$SERIAL"
# Phase 1 -- discover an existing active token on this device.
DEVICE_TOKEN=""
for USER_HOME in /Users/*; do
USER_NAME=$(basename "$USER_HOME")
[ "$USER_NAME" = "Shared" ] && continue
[ ! -d "$USER_HOME" ] && continue
id "$USER_NAME" >/dev/null 2>&1 || continue
CANDIDATES=$(sudo -u "$USER_NAME" -H /tmp/takumi-guard-setup.sh discover 2>/dev/null) || continue
while IFS= read -r CAND; do
[ -n "$CAND" ] || continue
STATUS=$(TG_BOT_ID="$BOT_ID" /tmp/takumi-guard-setup.sh verify "$CAND" 2>/dev/null)
case "$STATUS" in
active)
DEVICE_TOKEN="$CAND"
break 2
;;
unknown)
# Network down / API unreachable: abort instead of burning a
# fresh license under uncertainty.
echo "[Error] Could not verify token status against the Shisho Cloud API. Re-run after the API is reachable." >&2
rm -f /tmp/takumi-guard-setup.sh
exit 1
;;
esac
done <<EOF
$CANDIDATES
EOF
done
# Phase 2 -- if no active token exists yet, mint exactly one for the device.
if [ -z "$DEVICE_TOKEN" ]; then
DEVICE_TOKEN=$(TG_BOT_ID="$BOT_ID" /tmp/takumi-guard-setup.sh issue "$USER_IDENTIFIER")
if [ -z "$DEVICE_TOKEN" ]; then
echo "[Error] Failed to obtain device token" >&2
exit 1
fi
fi
# Phase 3 -- install the same token for every developer account.
for USER_HOME in /Users/*; do
USER_NAME=$(basename "$USER_HOME")
[ "$USER_NAME" = "Shared" ] && continue
[ ! -d "$USER_HOME" ] && continue
id "$USER_NAME" >/dev/null 2>&1 || continue
# Use zsh -lic (login + interactive) so that ~/.zshrc is loaded and
# package managers installed outside the default PATH are found.
sudo -u "$USER_NAME" -H zsh -lic "
/tmp/takumi-guard-setup.sh install '$DEVICE_TOKEN'
"
echo "[Done] $USER_NAME"
done
# Clean up credentials and temporary files
unset TG_BOT_API_KEY
rm -f /tmp/takumi-guard-setup.sh
Linux
#!/bin/bash
# Admin deployment wrapper (one token per device)
# TODO: Replace with your Bot ID and API key from Shisho Cloud console
BOT_ID="BTXXXXXXXXXXXXXXXXXXXXXXXXXX"
export TG_BOT_API_KEY="shisho_apikey_XXXXX"
# TODO: Update VERSION when a newer setup script becomes available
VERSION="0.5.0"
# Download the setup script
curl -sL -o /tmp/takumi-guard-setup.sh "https://shisho.dev/releases/takumi-guard-setup-${VERSION}.sh"
chmod 755 /tmp/takumi-guard-setup.sh
# Device-level USER_IDENTIFIER: serial number only.
SERIAL=$(dmidecode -s system-serial-number)
USER_IDENTIFIER="$SERIAL"
# Phase 1 -- discover an existing active token on this device.
DEVICE_TOKEN=""
for USER_HOME in /home/*; do
USER_NAME=$(basename "$USER_HOME")
[ ! -d "$USER_HOME" ] && continue
id "$USER_NAME" >/dev/null 2>&1 || continue
CANDIDATES=$(sudo -u "$USER_NAME" -H /tmp/takumi-guard-setup.sh discover 2>/dev/null) || continue
while IFS= read -r CAND; do
[ -n "$CAND" ] || continue
STATUS=$(TG_BOT_ID="$BOT_ID" /tmp/takumi-guard-setup.sh verify "$CAND" 2>/dev/null)
case "$STATUS" in
active)
DEVICE_TOKEN="$CAND"
break 2
;;
unknown)
echo "[Error] Could not verify token status against the Shisho Cloud API. Re-run after the API is reachable." >&2
rm -f /tmp/takumi-guard-setup.sh
exit 1
;;
esac
done <<EOF
$CANDIDATES
EOF
done
# Phase 2 -- if no active token exists yet, mint exactly one for the device.
if [ -z "$DEVICE_TOKEN" ]; then
DEVICE_TOKEN=$(TG_BOT_ID="$BOT_ID" /tmp/takumi-guard-setup.sh issue "$USER_IDENTIFIER")
if [ -z "$DEVICE_TOKEN" ]; then
echo "[Error] Failed to obtain device token" >&2
exit 1
fi
fi
# Phase 3 -- install the same token for every developer account.
for USER_HOME in /home/*; do
USER_NAME=$(basename "$USER_HOME")
[ ! -d "$USER_HOME" ] && continue
id "$USER_NAME" >/dev/null 2>&1 || continue
USER_SHELL=$(getent passwd "$USER_NAME" | cut -d: -f7)
sudo -u "$USER_NAME" -H "$USER_SHELL" -lic "
[ -f \"\$HOME/.bashrc\" ] && . \"\$HOME/.bashrc\" 2>/dev/null
/tmp/takumi-guard-setup.sh install '$DEVICE_TOKEN'
"
echo "[Done] $USER_NAME"
done
# Clean up credentials and temporary files
unset TG_BOT_API_KEY
rm -f /tmp/takumi-guard-setup.sh
Windows
Install for all users on the device
# Admin deployment wrapper (all-users, one token per device)
# Run as SYSTEM (or any administrator). Requires PowerShell 5.1 or later.
# TODO: Replace with your Bot ID and API key from Shisho Cloud console
$BotId = 'BTXXXXXXXXXXXXXXXXXXXXXXXXXX'
$env:TG_BOT_API_KEY = 'shisho_apikey_XXXXX'
# TODO: Update VERSION when a newer setup script becomes available
$Version = '0.5.0'
# Download the setup script
$ScriptPath = 'C:\Windows\Temp\takumi-guard-setup.ps1'
Invoke-WebRequest -Uri "https://shisho.dev/releases/takumi-guard-setup-$Version.ps1" `
-OutFile $ScriptPath -UseBasicParsing
# Device-level USER_IDENTIFIER: serial number only -- the token is shared
# across every user profile on this device.
$Serial = (Get-CimInstance -ClassName Win32_BIOS).SerialNumber
$UserIdentifier = $Serial
# Win32_UserProfile excludes built-in service profiles (SYSTEM, LocalService,
# NetworkService) via `Special = false`. Profiles whose directories no longer
# exist (deleted users with leftover registry entries) are also filtered out.
$Profiles = Get-CimInstance -ClassName Win32_UserProfile -Filter "Special = false" |
Where-Object { $_.LocalPath -and (Test-Path $_.LocalPath) }
# Phase 1 -- discover an existing active token on this device.
$DeviceToken = $null
:OuterDiscover foreach ($profile in $Profiles) {
$env:USER_HOME = $profile.LocalPath
$candidates = & powershell.exe -NoProfile -ExecutionPolicy Bypass -File $ScriptPath discover 2>$null
Remove-Item Env:USER_HOME -ErrorAction SilentlyContinue
if (-not $candidates) { continue }
foreach ($c in @($candidates)) {
if (-not $c) { continue }
$env:TG_BOT_ID = $BotId
$status = & powershell.exe -NoProfile -ExecutionPolicy Bypass -File $ScriptPath verify $c 2>$null
Remove-Item Env:TG_BOT_ID -ErrorAction SilentlyContinue
switch ($status) {
'active' {
$DeviceToken = $c
break OuterDiscover
}
'unknown' {
Write-Output "[Error] Could not verify token status against the Shisho Cloud API. Re-run after the API is reachable."
Remove-Item $ScriptPath -Force -ErrorAction SilentlyContinue
exit 1
}
}
}
}
# Phase 2 -- if no active token exists yet, mint exactly one for the device.
if (-not $DeviceToken) {
$env:TG_BOT_ID = $BotId
$DeviceToken = & powershell.exe -NoProfile -ExecutionPolicy Bypass -File $ScriptPath issue $UserIdentifier
Remove-Item Env:TG_BOT_ID -ErrorAction SilentlyContinue
if (-not $DeviceToken) {
throw "Failed to obtain device token"
}
}
# Phase 3 -- install the same token for every user profile.
foreach ($profile in $Profiles) {
$UserHome = $profile.LocalPath
$UserName = Split-Path $UserHome -Leaf
$env:USER_HOME = $UserHome
try {
& powershell.exe -NoProfile -ExecutionPolicy Bypass -File $ScriptPath install $DeviceToken
} catch {
Write-Output "[Error] Failed for $UserName : $_"
} finally {
Remove-Item Env:USER_HOME -ErrorAction SilentlyContinue
}
Write-Output "[Done] $UserName"
}
# Clean up credentials and the temporary script
Remove-Item Env:TG_BOT_API_KEY -ErrorAction SilentlyContinue
Remove-Item $ScriptPath -Force -ErrorAction SilentlyContinue
Security Considerations
- Bot API key handling: if compromised, immediately revoke it from the Shisho Cloud console. Previously minted tokens are not affected.
- Key rotation — After deploying to all target machines, rotate the bot API key in Shisho Cloud console as a preventive measure.
- Token revocation — If a token is compromised, revoke it from the Shisho Cloud console. Revocation takes effect within a maximum of 60 seconds.
Tips: Consider Running on a Schedule
The setup script is designed so that subsequent runs skip already-configured tools and reuse the existing valid token. That makes it well-suited for periodic execution from your management tool.
Running on a schedule lets you transparently handle cases like:
- A new developer joining the organization — setup propagates automatically once they log in to their machine
- A machine being reimaged or re-set-up — Guard configuration is restored without re-distributing manually
- A user accidentally deleting or overwriting the Guard configuration — the next run restores it
Daily to weekly cadence is reasonable in practice.